NEW - You can now accelerate your migration and modernization with AWS Transform. Read Getting Started in the AWS Transform User Guide.
Network requirements for Application Migration Service
Before you use Application Migration Service, make sure to prepare your environments. Preparation includes setting correct network settings, defining network requirements, and opening the correct ports.
Topics
Service and network architecture overview
Watch the AWS Application Migration Service -
Service architecture and network architecture video
This is the Application Migration Service network diagram:

Network setting preparations
As part of network setting preparations, set up a staging area and operational subnets.
Staging area subnet
Before setting up Application Migration Service you should create a subnet which will be used by the service as a staging area for data replicated from your source servers to AWS.
-
You must specify this subnet in the replication settings template. While you can use an existing subnet in your AWS account, the best practice is to create a new dedicated subnet for this purpose. Learn more about replication settings.
-
You can override this subnet for specific source servers in the replication settings.
Note
When planning to migrate to an AWS Local Zone, we recommend setting the staging area subnet within the AWS Region, and not the Local Zone. This ensures optimal launch conditions for the replication servers and conversion servers involved in the migration process. However, if you have specific requirements to use the Local Zone for the staging area subnet, we recommend performing thorough testing and validation to ensure you can successfully replicate and cut over your workloads without any issues.
Operational subnets
Test and cutover instances are launched in a subnet you specify in the Amazon EC2 launch template associated with each source server. The Amazon EC2 launch template is created automatically when you add a source server to AWS Application Migration Service.
Learn more about launching test and cutover instances.
Learn more about how Amazon EC2 launch templates are used.
Required connectivity settings
To prepare your network for running AWS Application Migration Service, configure the following connectivity settings. All communication is encrypted with TLS.
Important
SSL interception should not be applied for communication between replication servers and the Application Migration Service API endpoint, or between source servers and the Application Migration Service API endpoint.
Topics
Endpoints and firewall allowlist
Add the following endpoints and URLs to your firewall allowlist.
Application Migration Service API endpoints
| Protocol | Endpoint |
|---|---|
| IPv4 | https://mgn. |
| Dual-stack (IPv4/IPv6) | https://mgn. |
Replace region with the AWS Region code you are replicating
to (for example, us-east-1).
Amazon EC2 endpoint
The staging area subnet requires outbound access to the Amazon EC2 endpoint of its AWS Region.
Amazon S3 buckets
The AWS Replication Agent installer and the staging area subnet require access to Amazon S3. Allowlist these buckets:
https://aws-mgn-clients-<region>.s3.<region>.amazonaws.com/ https://aws-mgn-clients-hashes-<region>.s3.<region>.amazonaws.com/ https://aws-mgn-internal-<region>.s3.<region>.amazonaws.com/ https://aws-mgn-internal-hashes-<region>.s3.<region>.amazonaws.com/ https://aws-application-migration-service-<region>.s3.<region>.amazonaws.com/ https://aws-application-migration-service-hashes-<region>.s3.<region>.amazonaws.com/ https://amazon-ssm-<region>.s3.<region>.amazonaws.com/ https://al2023-repos-<region>-de612dc2.s3.<region>.amazonaws.com/
Note
For IPv6/dual-stack environments, use the Amazon S3 dual-stack endpoint format:
https://<bucket>.s3.dualstack.<region>.amazonaws.com/. Learn more about
Amazon S3
dual-stack endpoints.
Important
If your staging area subnet does not have outbound internet access, ensure that
your Amazon S3 VPC gateway endpoint policy allows access to the Amazon Linux 2023 package repository
bucket (al2023-repos-<region>-de612dc2).
Amazon S3 VPC Endpoint policy
If you use an Amazon S3 VPC Endpoint, you must provide sufficient permissions for service functionality, as shown in this example policy for replicating to us-east-1:
Communication between source servers and AWS Application Migration Service over TCP port 443
Each source server that is added to Application Migration Service must continuously communicate with the Application Migration Service API endpoint over TCP port 443.
The main operations performed through this route are:
-
Downloading and upgrading the AWS Replication Agent.
-
Connecting the source servers to the Application Migration Service console and displaying their replication status.
-
Monitoring the source servers for troubleshooting and resource consumption metrics (CPU, RAM).
-
Reporting source server-related events (for example, disk changes).
-
Transmitting source server information to the Application Migration Service console (hardware information, running services, installed applications and packages).
-
Preparing the source servers for test or cutover.
Communication between source servers and the staging area subnet over TCP port 1500
Each source server with an installed AWS Replication Agent continuously communicates with the replication servers in the staging area subnet over TCP port 1500. This port is used for the transfer of replicated data from the source servers to the staging area subnet.
The replicated data is encrypted and compressed when transferred over TCP port 1500. The data is encrypted on the source infrastructure before transfer and decrypted at the staging area subnet before being written to the volumes.
AWS Application Migration Service uses TLS 1.2 end to end from the agent installed on the source server to the Replication Server. Each replication server gets assigned a specific TLS server certificate, which is distributed to the corresponding Agent and validated on the agent side.
Communication between the staging area subnet and AWS Application Migration Service over TCP port 443
The replication servers in the staging area subnet must continuously communicate with Application Migration Service over TCP port 443. The main operations performed through this route are:
-
Downloading the replication software.
-
Connecting the replication servers to Application Migration Service and displaying their replication status.
-
Monitoring the replication servers for troubleshooting and resource consumption metrics.
-
Reporting replication-related events.
There are two ways to establish direct connectivity to the Internet for the VPC of the
staging area, as described in the
VPC FAQ
Troubleshooting connectivity issues
If there is no connection between your source servers and Application Migration Service, make sure that your corporate firewall enables connectivity from the source servers to Application Migration Service over TCP port 443. If the connectivity is blocked, enable it.
Enabling Windows Firewall for TCP port 443 connectivity
Important
The information provided in this section is for general security and firewall guidance only. The information is provided on "AS IS" basis, with no guarantee of completeness, accuracy or timeliness, and without warranty or representations of any kind, expressed or implied. In no event will AWS and/or its subsidiaries and/or their employees or service providers be liable to you or anyone else for any decision made or action taken in reliance on the information provided here or for any direct, indirect, consequential, special or similar damages (including any kind of loss), even if advised of the possibility of such damages. AWS is not responsible for the update, validation, or support of security and firewall information.
Note
These instructions are intended for the default OS firewall and allow outbound connectivity. You may still need to adjust other external components, such as firewall blocking or incorrect routes. Consult the documentation of any third-party local firewall you use.
-
On the source server, open the Windows Firewall console.
-
On the console, select the Outbound Rules option from the tree.
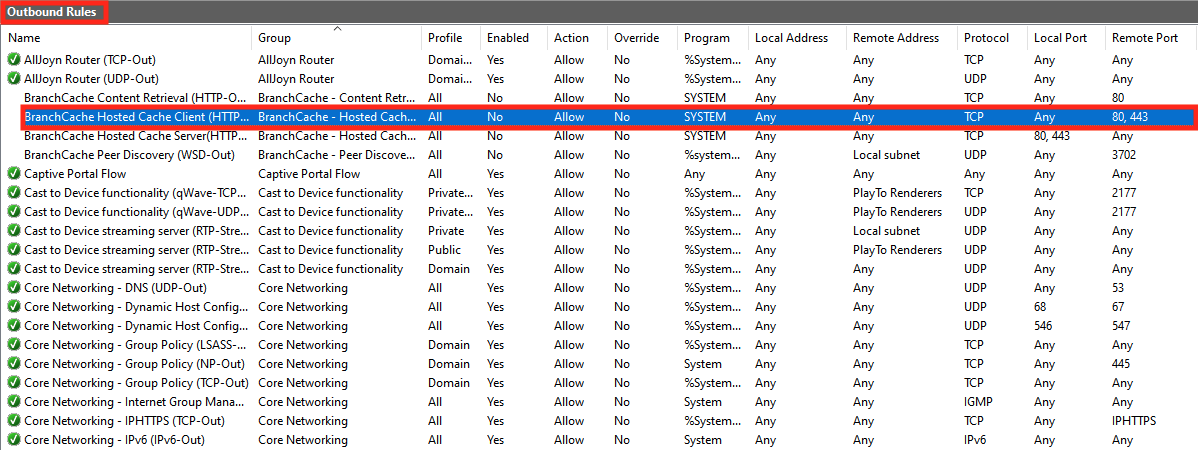
-
On the Outbound Rules table, select the rule that relates to the connectivity to Remote Port - 443. Check if the Enabled status is Yes.

-
If the Enabled status of the rule is No, right-click it and select Enable Rule from the pop-up menu.

Enabling Linux Firewall for TCP port 443 connectivity
-
Enter this command to add the required Firewall rule:
sudo iptables -A OUTPUT -p tcp --dport 443 -j ACCEPT -
To verify the creation of the Firewall rule, enter this command:
sudo iptables -LExpected output:
Chain INPUT (policy ACCEPT) target prot opt source destination Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination ACCEPT tcp -- anywhere anywhere tcp dpt:443